Online anonymity is a concept that is becoming more and more alien to us, and at the same time, in spite of it, an option more and more desirable. Some Tor 10 Browser want it for criminal reasons, others fear that their secrets (of state importance) may be disclosed and used for counterproductive purposes.
And still, others want anonymity online for a much more down-to-earth reason: to be able to troll to power in forums regardless of the consequences. The smallest percentage asks for privacy and anonymity for quite understandable reasons: because they feel that they simply deserve it “constitutionally”.
Regardless of all the above reasons, such persons have a chance to maintain anonymity and privacy on the Internet. For example, thanks to the Tor web browser, which has just got a stable version number as 10. Therefore,
Table of Contents
Below you will find step-by-step instructions on how to download and properly install Tor.
Our first step will be to go to the Torprojekt website, where we will be able to choose one in two versions of the browser. At the top, you will find a file intended for 64-bit systems
( 1 ), And at the bottom for 32-bit systems
( 2 ). From the drop-down list
( 3 ), We can still choose the software language we are interested in and we only need to download the file by clicking on the purple banner with the text Download
( 4 ). If we are using a system other than Windows, we will have to choose our target OS
( 5 ) Before downloading.
How do I install and run Tor Browser?
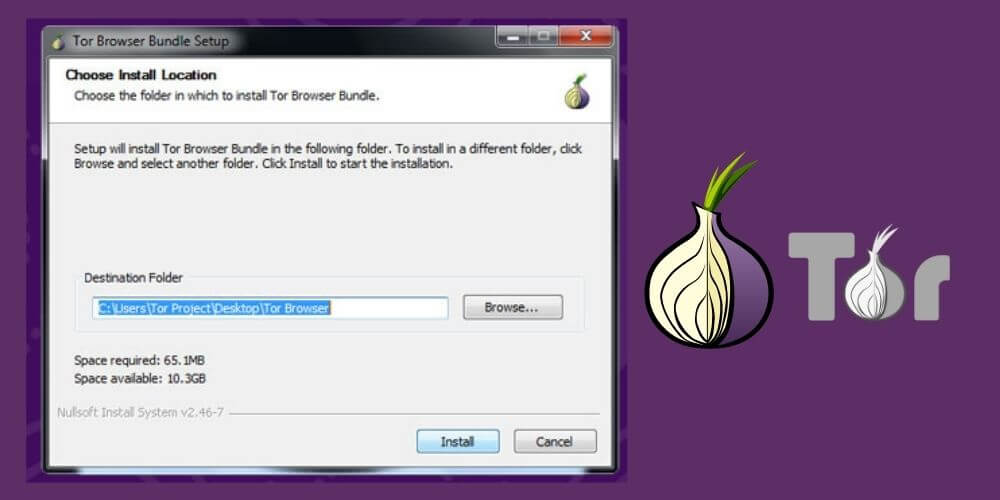
After downloading the file with the .exe extension and 53.4 MB in size, we will have to run it. The installation starts with a question about the choice of language, but if we selected during the download, now our native language should be the default choice.
So we accept the English language by clicking OK and going to the board in the selection of the installation folder. The application wants to ultimately install itself on the desktop
( 6 ) And it is also worth letting it settle there . It is in vain to choose the path C: \ Program Files (x86), where other programs usually install. Tor will throw an error and we will have to let it install on the desktop or choose another place on our computer.
After the installation has been properly performed, we will have to find the folder that we previously selected for the application, and if it was the desktop, we will also find an icon titled Start Tor Browser there, which will launch the browser.
So we click on the mentioned icon twice – this will start the program for the first time, and thus the Tor network connection window. We have two options to choose from: Configure
( 7 ) Connect

( 8 ). We are only interested in Connect because we do not have to configure the connection for a simple reason: Tor is not blocked in our country, as it is in Egypt, China, or Turkey.
How do I connect to Tor network?
After clicking Connect, a connection establishing window will appear, in which we will be informed that this action may take up to several minutes. In practice, however, it only takes a few seconds, then the window disappears and we see a completely new one, this time belonging to the actual Tor browser.
By default, it will occupy an area of about half the screen, and if we want to maximize the window, we will get information that increasing the Tor browser will allow websites to set the screen size and thus track the user.
By now, we have probably already noticed that version 10 of the browser is not necessarily in its entirety, so the sense of entering into the discussion of ( 9 ) subsequent browser elements such as Privacy, Network, Security or Additional Services exists only when we know English. In a nutshell, the browser provides the highest standard of privacy and security while surfing.
Thanks to it, we are protected against spying, surveillance and censorship. We’ll also learn that Tor isolates cookies and clears the history after an Internet browsing session.
How does Tor work simply ?
The following introductory sentences also explain how Tor works. Every time we visit a domain, our traffic is routed and encrypted in a circuit of three Tor relays (three computers) around the world, each with a naturally different IP address and other critical parameters.
As a result, no website knows where we are connecting from. At any time, we can request a new circuit by selecting the New circuit for this page from the menu in the upper right corner
(10). By using the keyboard shortcut Ctrl + Shift + L.
Clicking the icon and in the circle next to the address bar ( 11), we will be able to see what computers are encrypting our location on a given page at that moment.
Tor browser, which enables anonymous surfing on the web, made its debut in version 10.
The Tor browser provides security on three levels, which we can set ourselves at any time. These levels are Standard (all features of the Tor browser and websites are enabled),
More secure (Javascript support on non-HTTPS sites is disabled, similarly some fonts and symbols, and HTML5 media – audio and video – start only after our click).
The most secure (same situation with HTML5 as above, and JavaScript disabled by default on all pages, same with some fonts, symbols and pictures).
Read Also : How to Clear Cache in Internet Browsers?
These options can be set, for example, in the aforementioned review at the start ( 12) or by clicking on the onion icon in the extreme upper left corner of the browser.
By hovering over it with the mouse cursor, we will also get a prompt whether Tor is currently connected. When using the Tor browser, we must prepare for the fact that surfing the web will be slower than with traditional browsers.
Tor Browser Version 10 How to Install & Setup Tor Safely In 2021
Is Tor safe to use?
All because the data must not only be x-rayed by the application for security, but also have to travel for a longer time, because through the aforementioned circuit of three computers scattered around the world.
Depending on the level of security we have set up, some elements on the pages may also not be displayed to us, as well as entire pages. So, the track has its undeniable advantages, which are accompanied by disadvantages that cannot be separated.
Tor does not recommend but also does not require the installation of, AdBlock-style extensions, as it blocks unwanted windows and advertisements by itself.
Should I use VPN with Tor?
It is also not recommended for less experienced users to use Tor with a VPN. However, if you know your stuff, it is worth checking out Tor’s help before attempting to do such acrobatics, which discusses how to use a VPN.
Similarly, it is not recommended to use the Torrent browser to download torrents, because, as we read on the Tor project blog , it may result in an external attack that exposes us to our true location.
CONCLUSION
Finishing this short guide for novice internet users who want anonymity on the web, I can only wish you safe surfing without annoying pop-up windows, tons of cookies, and annoying ads claiming that we won a new iPhone for the hundredth time.
We are always open to your problems, questions, and suggestions, so feel free to Comment on us by filling this. This is a free service that we offer, We read every message we receive. Tell those we helped by sharing our posts with friends or just liking to Follow us on Instagram, Twitter and join our Facebook Page or contact us on Gmail, Linkedin, etc

Pradeep Sharma is a author the mind behind Techjustify, where I craft insightful blogs on technology, digital tools, gaming, AI, and beyond. With years of experience in digital marketing and a passion for tech innovation, I aim to simplify complex topics for readers worldwide.
My mission is to empower individuals with practical knowledge and up-to-date insights, helping them make informed decisions in the ever-evolving digital landscape.

